What STASHit solves for you!
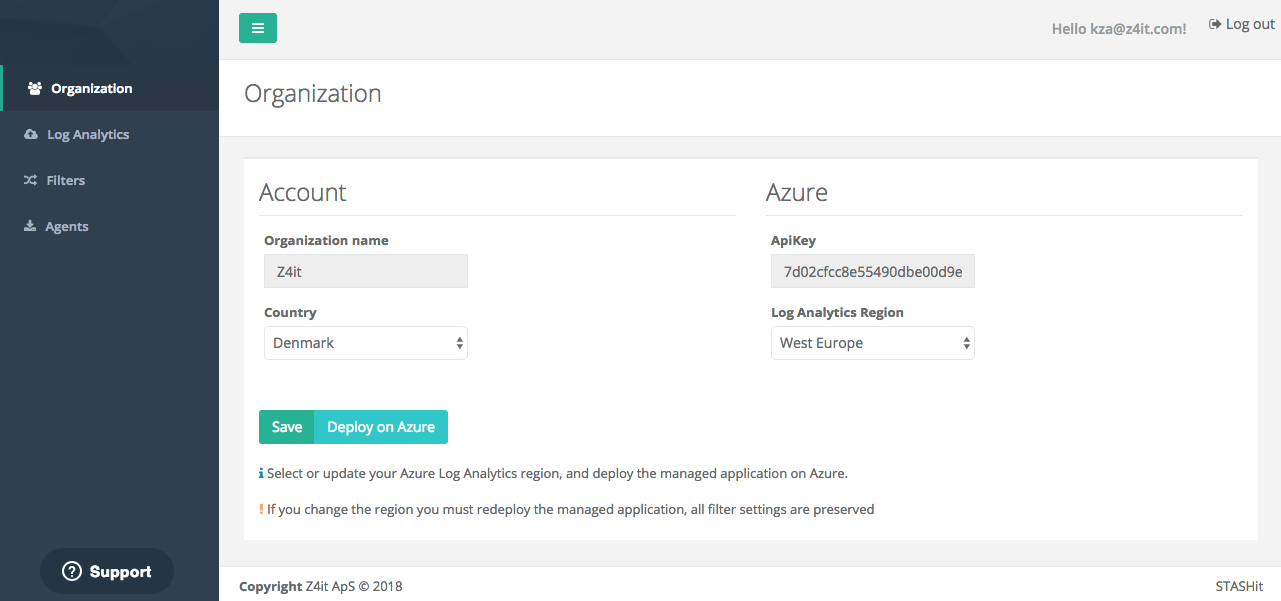
Need to log events like password resets, access to specific folders or files to comply to your internal compliance or GDPR rules? No problem. Save your events in a dedicated long term Microsoft Azure Log Analytics workspace.
Are you already using Microsoft Azure Log Analytics but missing your clients event logs? Simply deploy the MSI based agent(s) and you got them, even when users are traveling or working at home.
We have not seen any public available applications that can do this in our research. So keep reading and see how you get the most out of your windows events.
Discover great features
Security
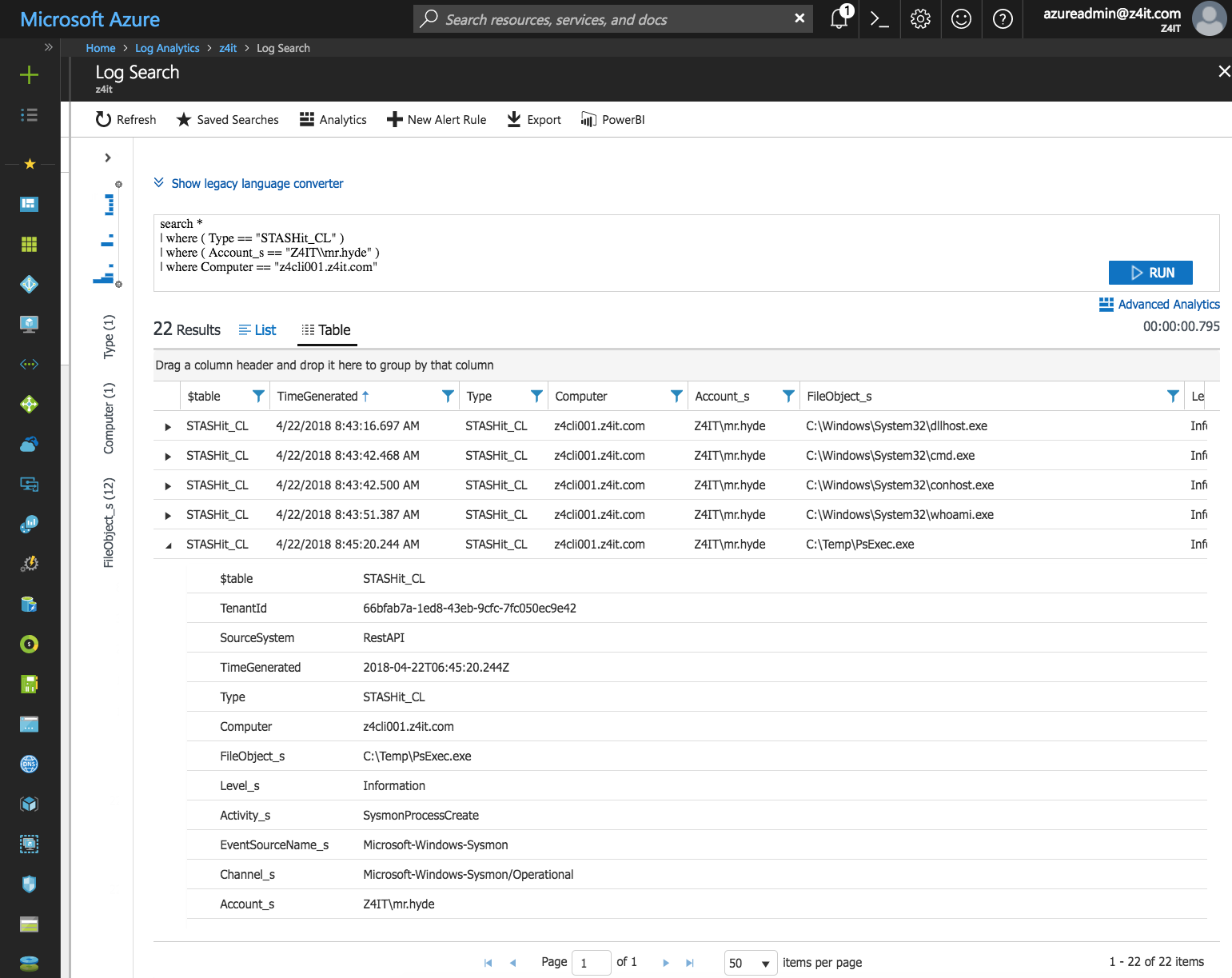
Detect the hackers or abnormal system patterns?, Sysmon by Microsoft is included so get commands like “whoami.exe” logged in Microsoft Azure Log Analytics for forensic analysis of attacks or troubleshooting.
Traceablity
Need to trace user activity across systems? All events with user identification information is enriched with the username in a dedicated field, for fast and easy traceability across systems and event types.
Economy
Want to save a lot of both space and money on you Microsoft Azure Log Analytics bill?. As events are throttled and filtered you only store what you need. Typically events are reduced by 99,5%.
Extendable
Missing an event?, simply create a support ticket and we will created the matching filter for it at no cost. Everyone benefits when the event filter database is expanded.
And much more
Simple
Select in a single view the events you want to store, and determine how long you would like to store them for, and that’s it! After a few minutes you will start receiving the events in Microsoft Azure Log Analytics.
Economy
Want to get your servers security logs in Microsoft Azure Log Analytics, but find the OMS pricing option a bit expensive? STASHit is just as good when used in the standalone pricing tier in Microsoft Azure Log Analytics.
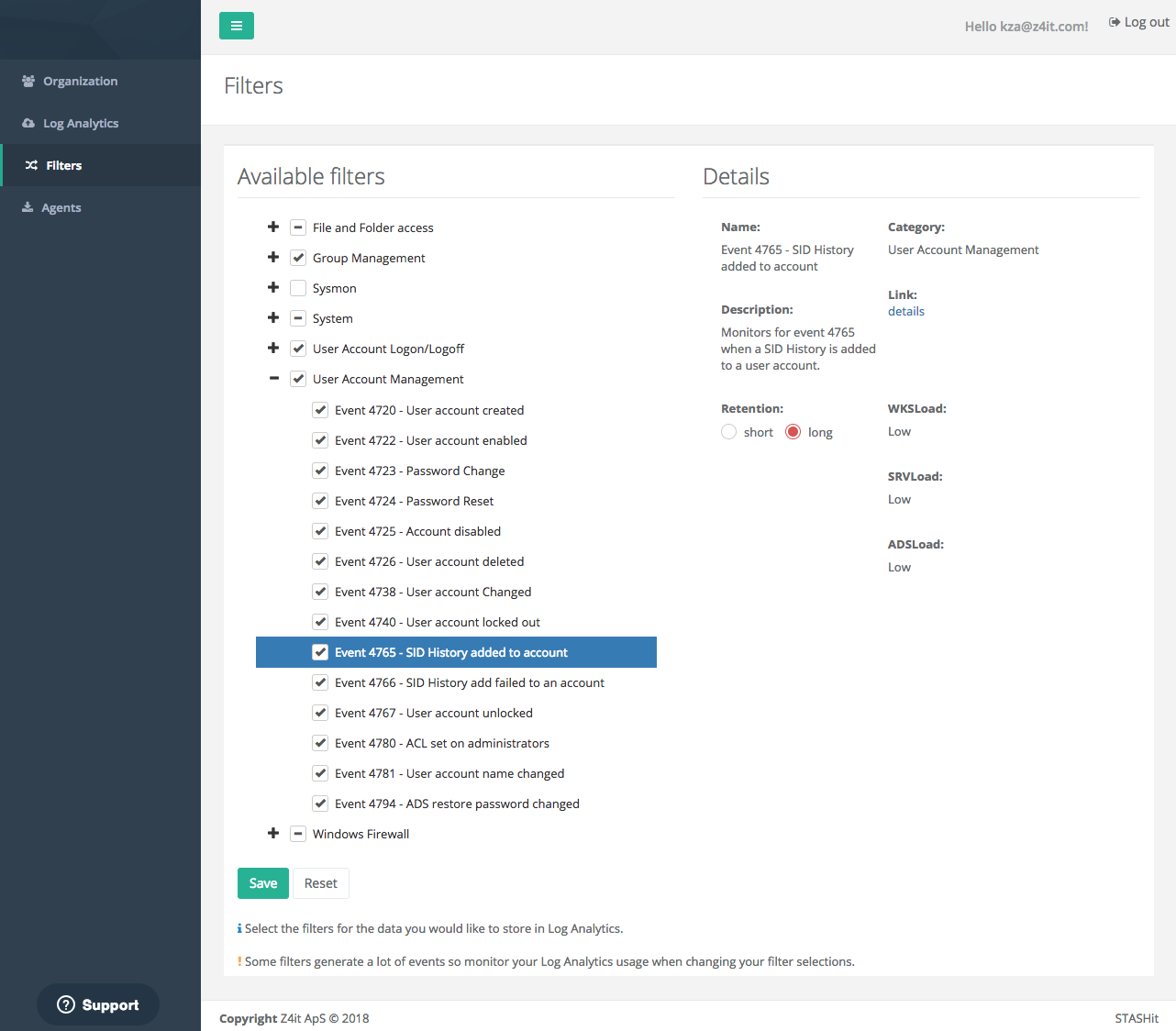
Deep filtering
Deep filter on specific events. You might need to store an event like ‘An account failed to log on’ but only when the username is correct to detect if someone is trying to guess a password.
Agents
Don't want to install third-party agents on Domain Controllers or other critical servers/systems? No problem! STASHit works fine with Windows Event Forwarding (WEF). Windows Event Forwarding is easy to setup by Group Policy and then have the STASHit agent installed on the WEF server only.